For decades, cybersecurity relied on a deceptively simple idea: build a strong wall around your network. Companies invested billions in “Castle and Moat” strategies, deploying firewalls, VPNs and perimeter defenses to protect internal systems. The logic was clear: if an attacker couldn’t get inside the network, the data was safe. In this world, the IP address was your passport, and being “on the corporate network” was the ultimate badge of trust.
Yet, as we move through 2026, that model has fundamentally collapsed. Modern infrastructure— defined by public clouds, microservices, remote global workforces and thousands of interconnected APIs—has dissolved the traditional network boundary. The perimeter hasn’t just been breached; it has disappeared. Once an attacker bypasses the “front door,” they can often move freely across internal systems. This is why the industry is undergoing a massive shift toward Zero-Trust Networking, where the network itself is no longer the boundary. Instead, Identity is the new perimeter.
The Hotel Keycard: Understanding Micro-Segmentation
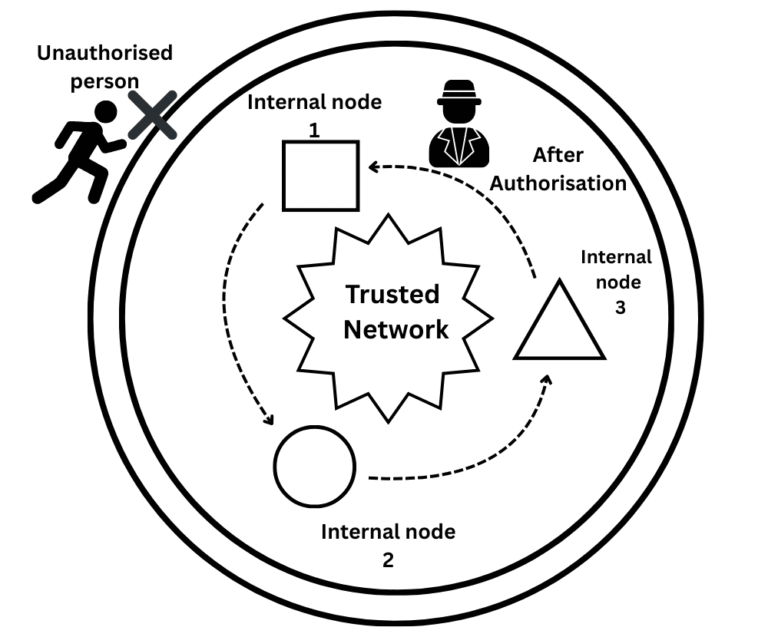
To understand why traditional firewalls fail, consider the analogy of a luxury hotel. A traditional firewall is like the front door of the hotel. Once a person passes the lobby, they are “inside.” In a legacy network, that person could potentially try every room door in the hallway. Micro-segmentation, the heart of Zero Trust, changes this. It is like giving every guest a digital keycard that only works for their specific room and the elevator to their floor.
Even if a malicious actor gets into the “lobby” of your cloud network, they remain trapped. They cannot “see” the database server or the payment gateway because they lack the specific cryptographic identity required even to acknowledge that those services exist. In the Zero Trust era, we treat every microservice as if it were on the open internet, requiring its own “room key” for every interaction.
Enter Zero-Trust: Never Trust, Always Verify
Zero-Trust flips the traditional model on its head by removing the concept of a “trusted zone.” It operates on the core principle: Never trust, always verify. In this world, no request is granted access based on where it comes from (its IP address or network segment). Instead, every request must prove its identity, its intent and its security posture before a single packet of data is exchanged.
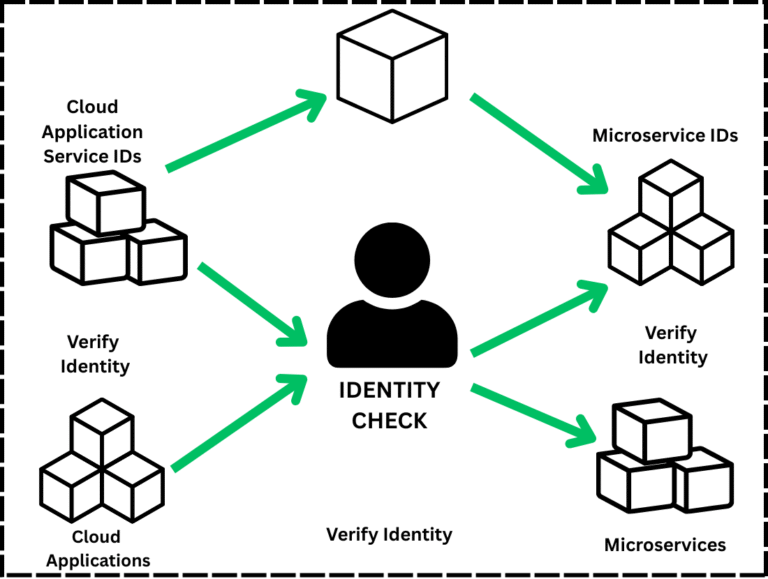
This leads us to Identity-Based Networking. Instead of identifying a database as “10.0.5.21,” we identify it as “Production-DB-Cluster-01.” Each service is issued a unique, verifiable and cryptographic identity. This identity acts as a continuous fingerprint. Whether that service is running on an on-premise server or a Lambda function in AWS, its identity remains constant, allowing for security policies that are human-readable and mathematically provable.
Shows the “proof” stage where two services verify each other’s cryptographic certificates.
From Brittle IPs to Cryptographic Truth
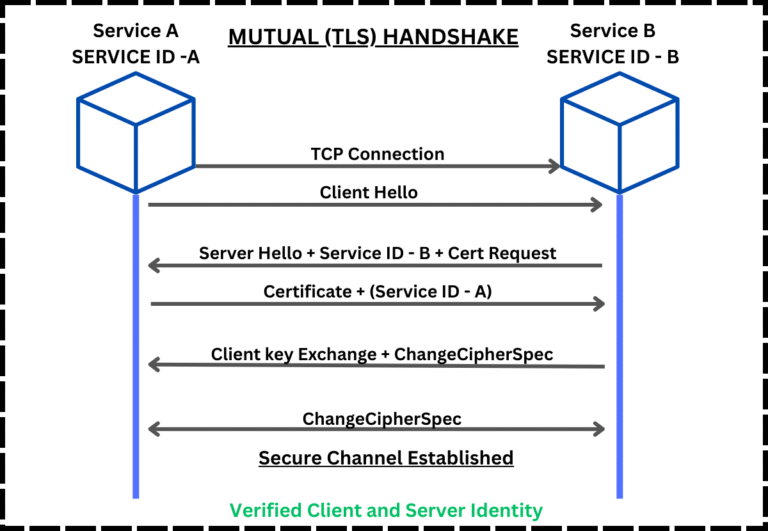
Traditional networking relies on brittle identifiers like IP addresses and ports. In a modern Kubernetes cluster, a Pod may have a different IP address each time it restarts. Relying on an IP-based firewall rule in this environment is a recipe for disaster. Identity-based networking replaces this chaos with Mutual TLS (mTLS) and service identities.
When Service A wants to talk to Service B, they perform a cryptographic handshake. They don’t just check if the IP is allowed; they exchange certificates to prove they are exactly who they claim to be. This ensures that:
- Authentication is absolute:You know exactly which service is calling.
- Authorization is granular:You can specify that “only the Billing Service can write to the Ledger Database.”
- Encryption is default:All data in transit is encrypted by the very nature of the identity handshake.
The 2026 Tech Stack: SPIFFE, SPIRE, and Service Meshes
Implementing this at scale requires specialized tools. In 2026, the gold standard for workload identity is SPIFFE (Secure Production Identity Framework for Everyone) and its runtime, SPIRE. These tools act as an automated “ID Office” for your software, issuing short-lived, rotated certificates to every process in your system.
To manage these identities without burdening developers, organizations use service meshes such as Istio or Linkerd. These platforms act as a transparent “security sidecar” that automatically handles mTLS handshakes and policy enforcement. This allows developers to focus on writing code while the platform ensures that every connection is secure, authenticated, and logged.
Provides the technical blueprint of how identities are issued and verified in real-time.
The “Blast Radius” and the End of Lateral Movement
The most significant benefit of this shift is the drastic reduction of the “Blast Radius.” In a traditional breach, the goal of the attacker is Lateral Movement; jumping from a compromised web server to a high-value database. In an identity-centric network, a compromised node is an island, not a gateway.
Because the “Database” service will only accept connections from a service presenting a valid “Payment-Service” certificate, the attacker’s stolen network access is useless. They can ping the IP all they want, but without the cryptographic identity, the database remains invisible and unreachable. We have effectively moved from “securing the network” to “securing the data.”
Teaching the New Perimeter
We may tell our younger generation that the networking textbooks from 2010 are becoming historical artifacts. Ten years ago, the pinnacle of networking skill was mastering Cisco CLI and subnetting. Today, those are foundational but insufficient. To be an architect in 2026, you must understand Identity Architecture.
We must stop thinking about “where” a server is and start thinking about “what” a server is. If you can define the identity and the allowed relationships of a system, the physical network becomes irrelevant. We are moving from a world of “hardware mechanics” to “logic architects.”
Conclusion: Identity is the Only Perimeter Left
The shift to Zero-Trust is no longer optional. Major organizations like Google, Netflix and Microsoft have already moved away from perimeter-based security because they realized that in a cloud-native world, the “wall” is a myth. The network itself is no longer a trust boundary; it is merely a transport layer.
The future of infrastructure security is not about building stronger walls or taller fences. It is about verifying every connection, every service, and every request with mathematical certainty. Your firewall is not the perimeter anymore. In 2026 and beyond, Identity is the only perimeter that matters.
